High quality Cisco CCNA Security 210-260 dumps pdf files and vce youtube demo update free shared. Get the newest Cisco CCNA Security 210-260 dumps exam training resources in PDF format free download freom leads4pass. “Implementing Cisco Network Security” is the name of Cisco CCNA Security https://www.leads4pass.com/210-260.html exam dumps which covers all the knowledge points of the real Cisco exam, 100% pass guarantee.
Prepare for Cisco 210-260 exam with latest Cisco CCNA Security 210-260 dumps exam questions and answers download free try from leads4pass. The best and most updated useful Cisco CCNA Security 210-260 dumps pdf training materials, pass Cisco 210-260 exam test easily at the first time.
High quality Cisco 210-260 dumps pdf files free download: https://drive.google.com/open?id=0B_7qiYkH83VRcnI0SE83bHBvQ1k
High quality Cisco 210-065 dumps pdf files free download: https://drive.google.com/open?id=0B_7qiYkH83VRODRqVmVBYWxuc0k
QUESTION 1
How can you detect a false negative on an IPS?
A. View the alert on the IPS.
B. Review the IPS log.
C. Review the IPS console.
D. Use a third-party system to perform penetration testing.
E. Use a third-party to audit the next-generation firewall rules.
Correct Answer: D
QUESTION 2
How can FirePOWER block malicious email attachments?
A. It forwards email requests to an external signature engine.
B. It scans inbound email messages for known bad URLs.
C. It sends the traffic through a file policy.
D. It sends an alert to the administrator to verify suspicious email messages.
Correct Answer: C
QUESTION 3
Which tool can an attacker use to attempt a DDoS attack?
A. botnet
B. Trojan horse
C. virus
D. adware
Correct Answer: A
QUESTION 4
Which two statements about stateless firewalls are true? 210-260 dumps (Choose two.)
A. They compare the 5-tuple of each incoming packet against configurable rules.
B. They cannot track connections.
C. They are designed to work most efficiently with stateless protocols such as HTTP or HTTPS.
D. Cisco IOS cannot implement them because the platform is stateful by nature.
E. The Cisco ASA is implicitly stateless because it blocks all traffic by default.
Correct Answer: AB
QUESTION 5
Which three ESP fields can be encrypted during transmission? (Choose three.)
A. Security Parameter Index
B. Sequence Number
C. MAC Address
D. Padding
E. Pad Length
F. Next Header
Correct Answer: DEF
QUESTION 6
In the router ospf 200 command, what does the value 200 stand for?
A. process ID
B. area ID
C. administrative distance value
D. ABR ID
Correct Answer: A
QUESTION 7
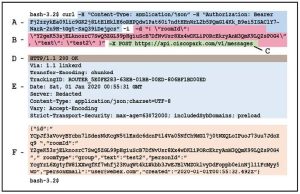
Refer to the exhibit.

Which statement about the given configuration is true?
A. The single-connection command causes the device to establish one connection for all TACACS transactions.
B. The single-connection command causes the device to process one TACACS request and then move to the next server.
C. The timeout command causes the device to move to the next server after 20 seconds of TACACS inactivity.
D. The router communicates with the NAS on the default port, TCP 1645.
Correct Answer: A
QUESTION 8
What is example of social engineering
A. Gaining access to a building through an unlocked door.
B. something about inserting a random flash drive.
C. gaining access to server room by posing as IT
D. Watching other user put in username and password (something around there)
Correct Answer: C
QUESTION 9
In which three ways does the TACACS protocol differ from RADIUS? 210-260 dumps (Choose three.)
A. TACACS uses TCP to communicate with the NAS.
B. TACACS can encrypt the entire packet that is sent to the NAS.
C. TACACS supports per-command authorization.
D. TACACS authenticates and authorizes simultaneously, causing fewer packets to be transmitted.
E. TACACS uses UDP to communicate with the NAS.
F. TACACS encrypts only the password field in an authentication packet.
Correct Answer: ABC
QUESTION 10
What can the SMTP preprocessor in FirePOWER normalize?
A. It can extract and decode email attachments in client to server traffic.
B. It can look up the email sender.
C. It compares known threats to the email sender.
D. It can forward the SMTP traffic to an email filter server.
E. It uses the Traffic Anomaly Detector.
Correct Answer: A
QUESTION 11
Which option is the most effective placement of an IPS device within the infrastructure?
A. Inline, behind the internet router and firewall
B. Inline, before the internet router and firewall
C. Promiscuously, after the Internet router and before the firewall
D. Promiscuously, before the Internet router and the firewall
Correct Answer: A
QUESTION 12
Which two authentication types does OSPF support? (Choose two.)
A. plaintext
B. MD5
C. HMAC
D. AES 256
E. SHA-1
F. DES
Correct Answer: AB
High quality Cisco CCNA Security 210-260 dumps pdf training resources which are the best for clearing https://www.leads4pass.com/210-260.html exam test, and to get certified by Cisco CCNA Security. Helpful Cisco CCNA Security 210-260 dumps exam is omnipresent all around the world, download one of the many PDF readers that are available for free.
High quality Cisco CCNA Security 210-260 dumps vce youtube demo: https://youtu.be/seDmEyXcd3w